One Of The Best Info About How To Prevent Ip Spoofing

Do not authenticate devices and users solely.
How to prevent ip spoofing. Make an acl of ip. To prevent yourself from ip spoofing negative consequences, you should check the following methods of protection: Configuration and services that are vulnerable to ip spoofing:
Here are some steps companies can take: Up to 20% cash back the options to protect against ip spoofing include: <<strong>ip</strong>_address> and are the ip address and domain of the other email system that sends mail on.</p>
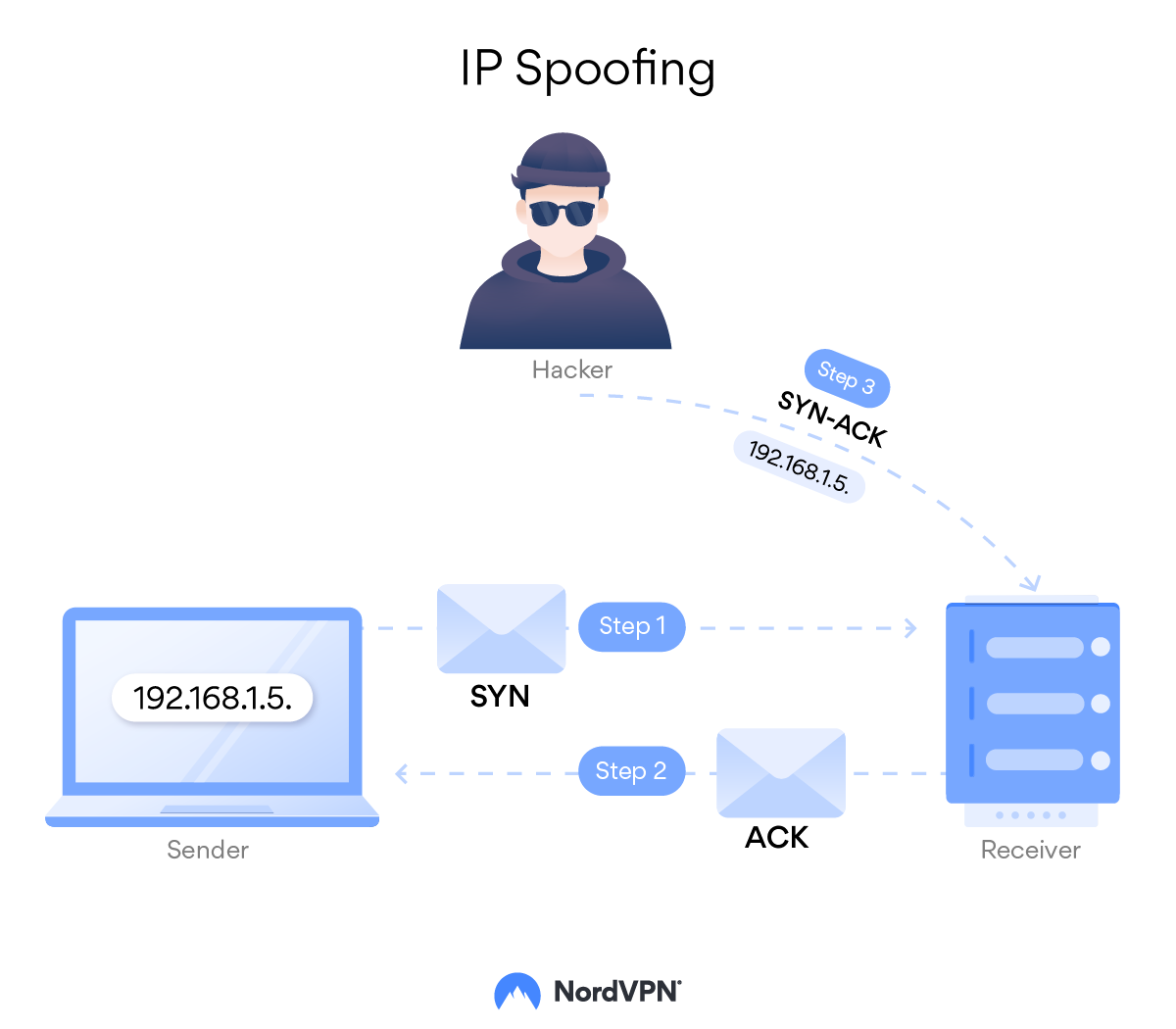
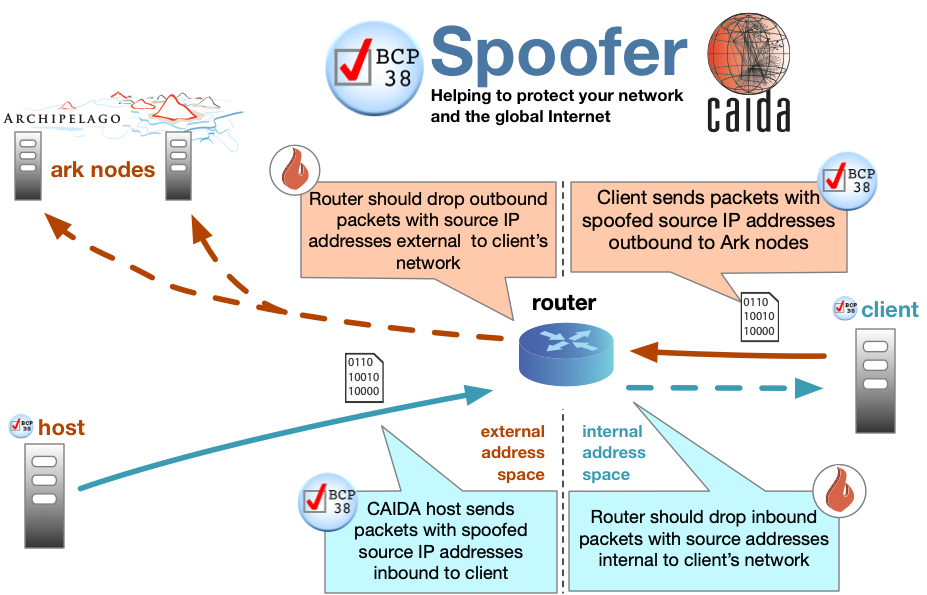
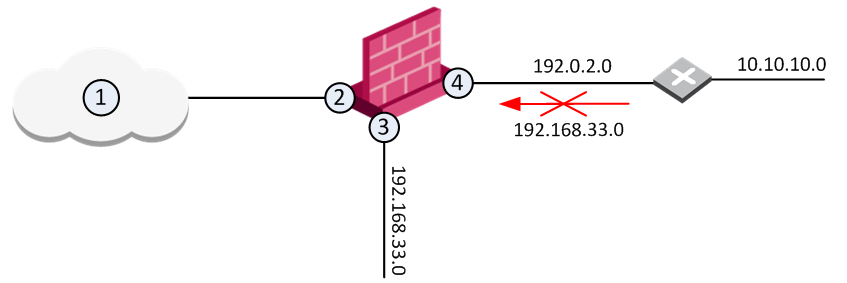
The r services suite (rlogin, rsh,. There are a few ways to add roadblocks between a hacker and a potential target. Packet filtering / ingress filtering.
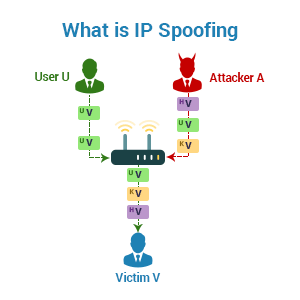
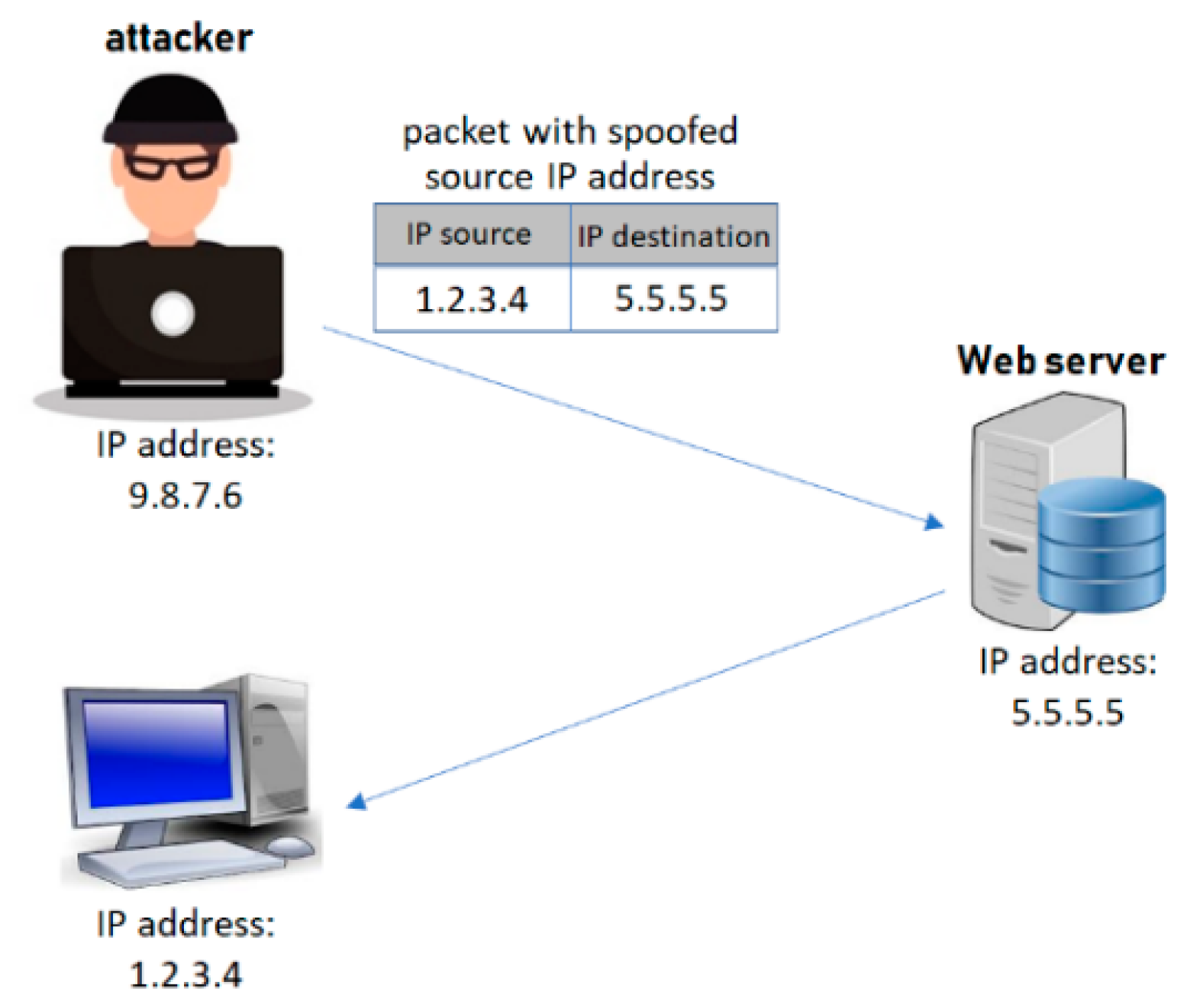
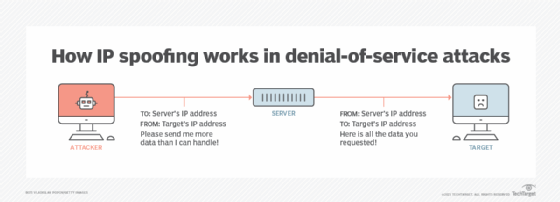
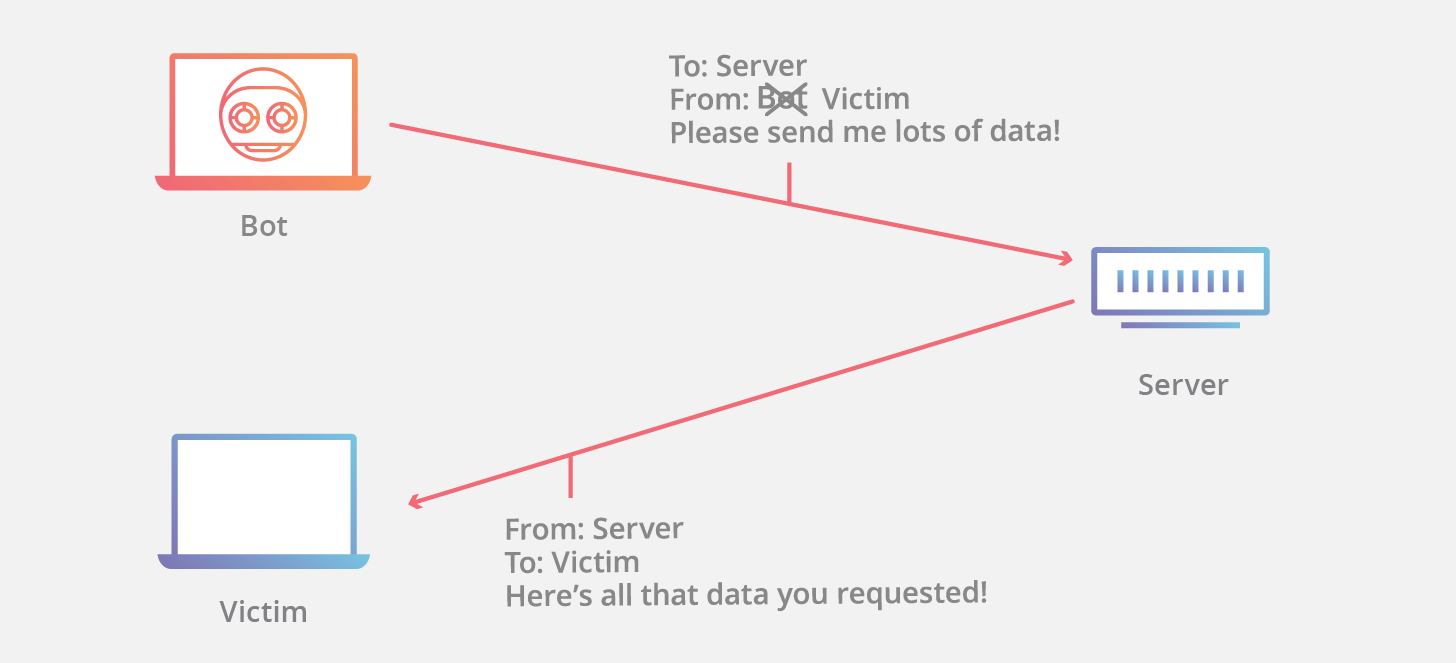
Up to 20% cash back whereas email spoofing focuses on the user, ip spoofing is primarily aimed at a network. Use strong verification and authentication methods for all remote access. Another effective way to prevent ip spoofing involves configuring routers and switches to deny them entry to packets from outside your local network.
You'll have no idea where the problem originates. Block the ip address that seems to be the source, and you'll block work from a benign computer. Every device or user attempting to join a network has its ip packets examined.
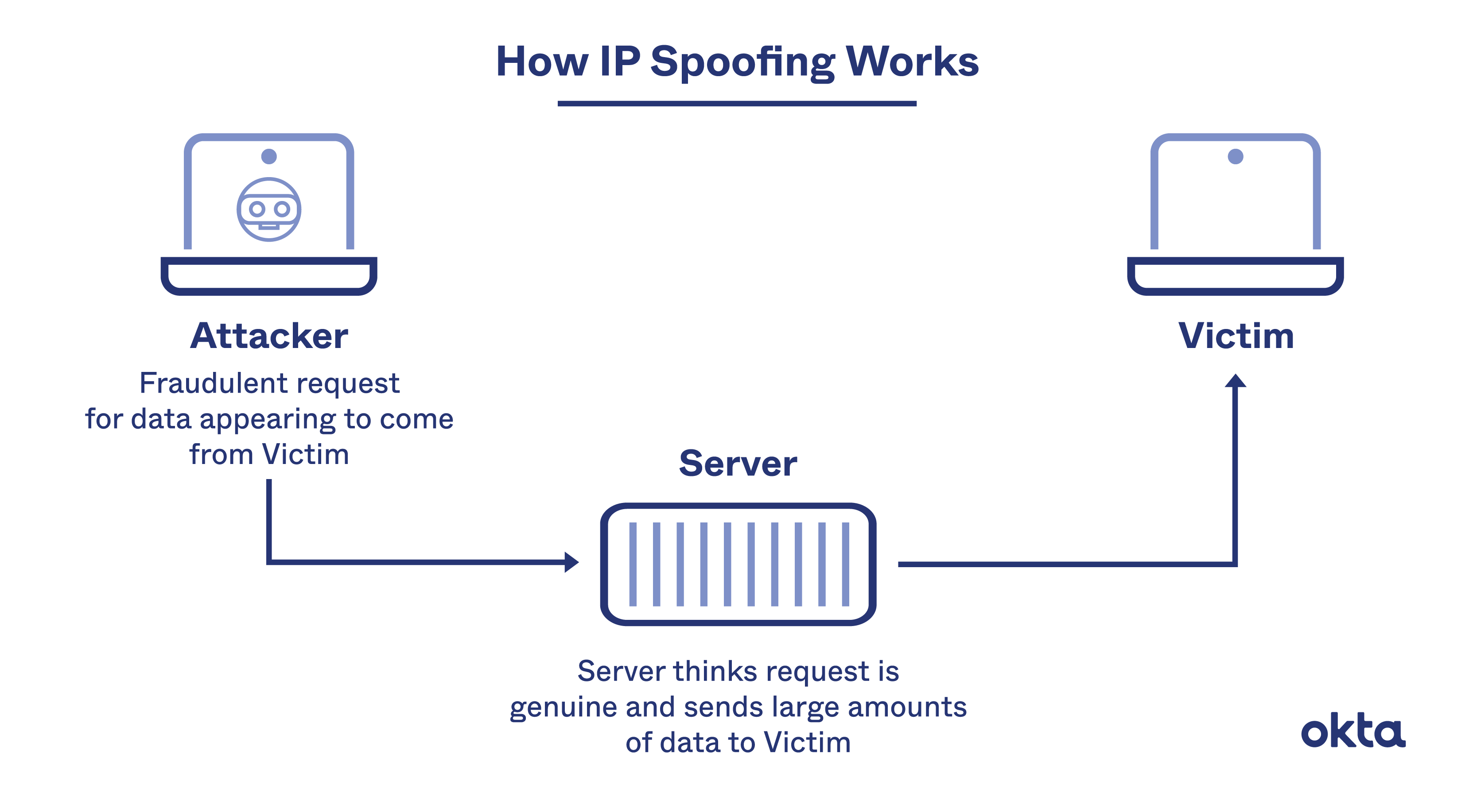
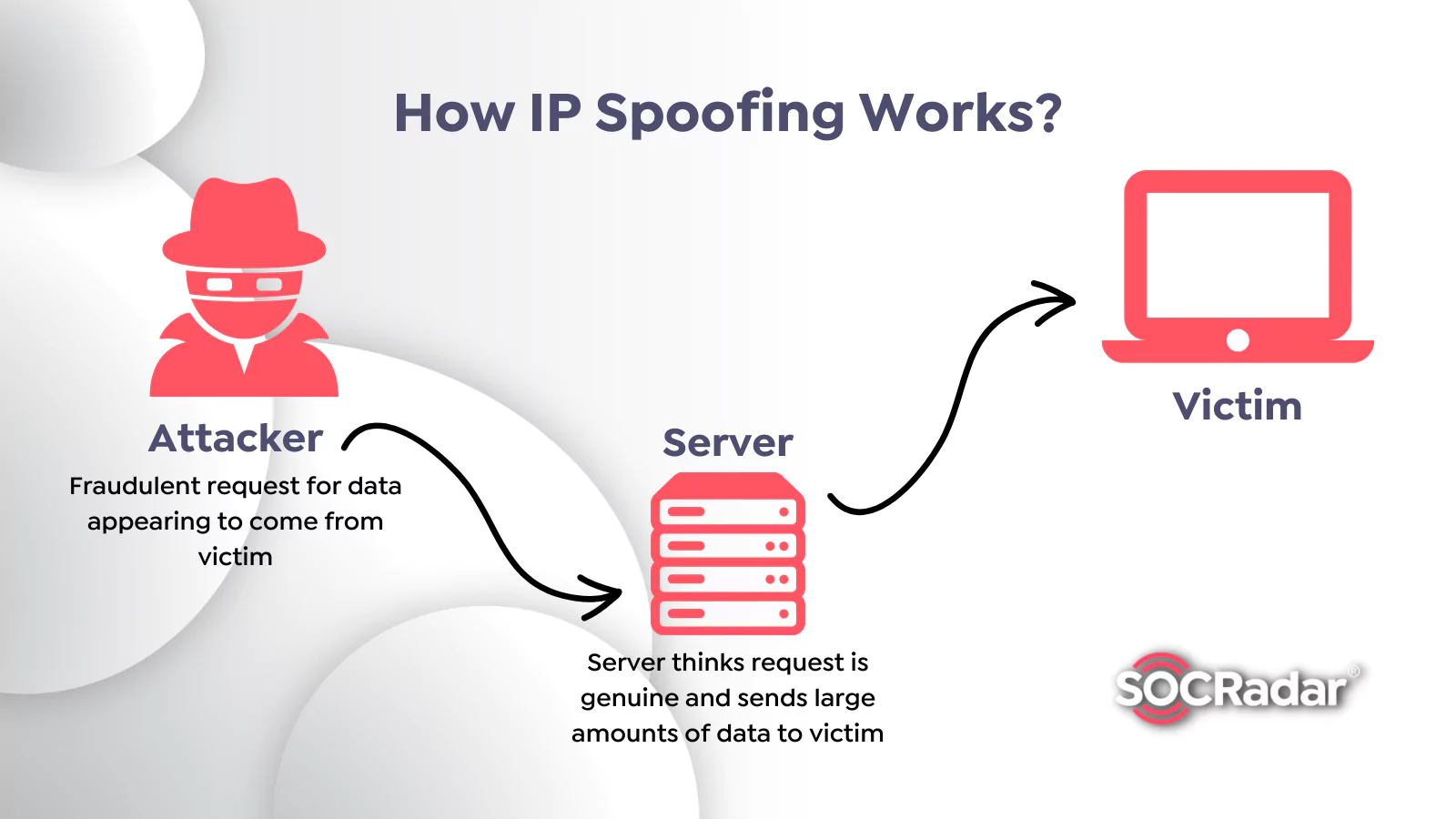
Monitoring networks for atypical activity. Rpc (remote procedure call services)any service that uses ip address authentication; Ip spoofing involves an attacker trying to gain unauthorized access to a.
Since ip address #12 isn't in contoso.com's spf txt record, the message fails the spf check and the receiver may choose. Then, monitor your network for suspicious activity with a firewall, which uses a packet filter that inspects ip packet headers. Monitor networks for unusual activity.
Ip spoofing protection for it specialists includes: To help prevent ip spoofing, you should use a vpn to hide your ip address. Suppose a phisher finds a way to spoof contoso.com:
Deploying packet filtering to detect inconsistencies (such as outgoing.