Fantastic Tips About How To Start Dos Attack
Mac flooding will disrupt layer.
How to start dos attack. 🔵 edureka cyber security masters program: This should display the desired target. So use the below command to.
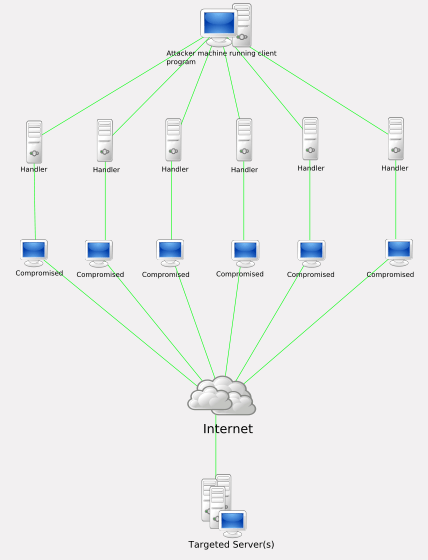
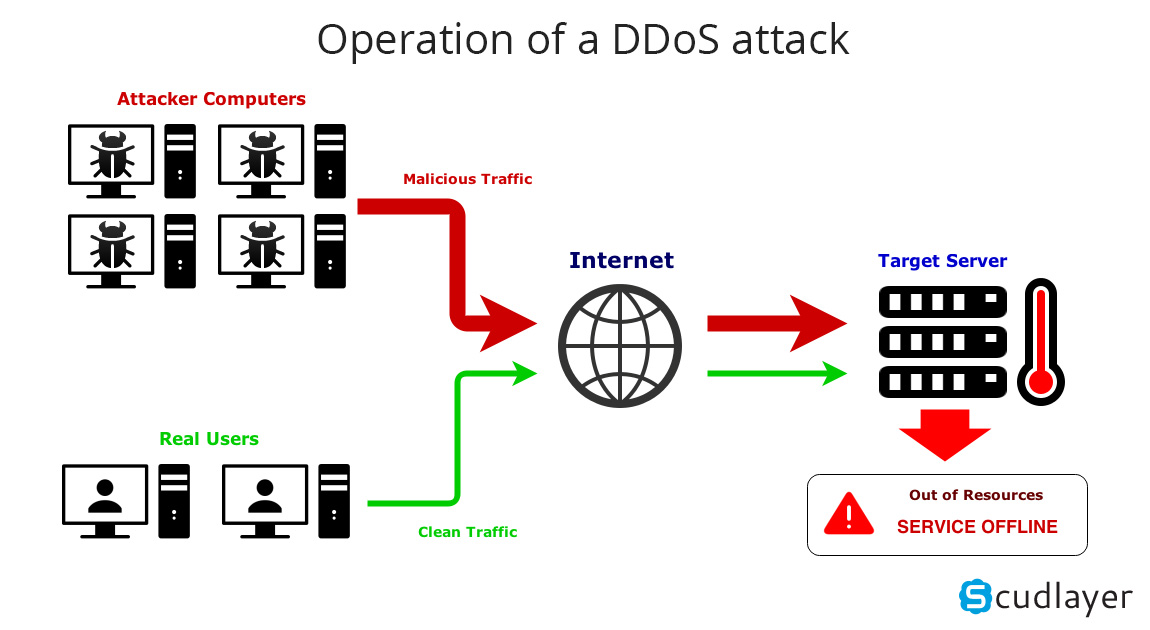
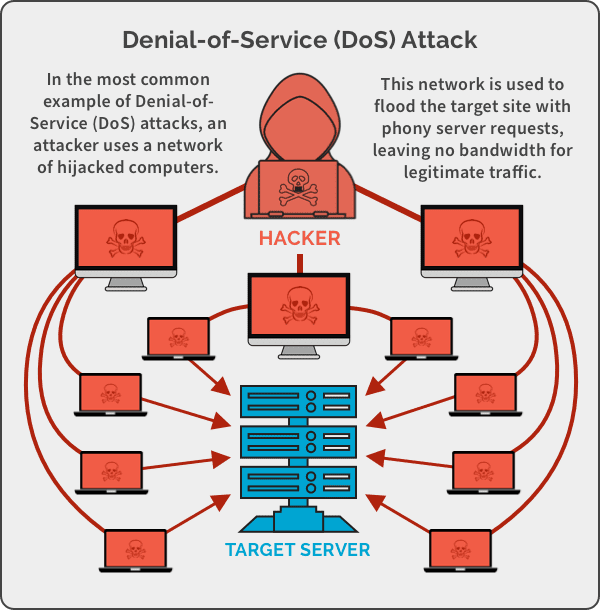
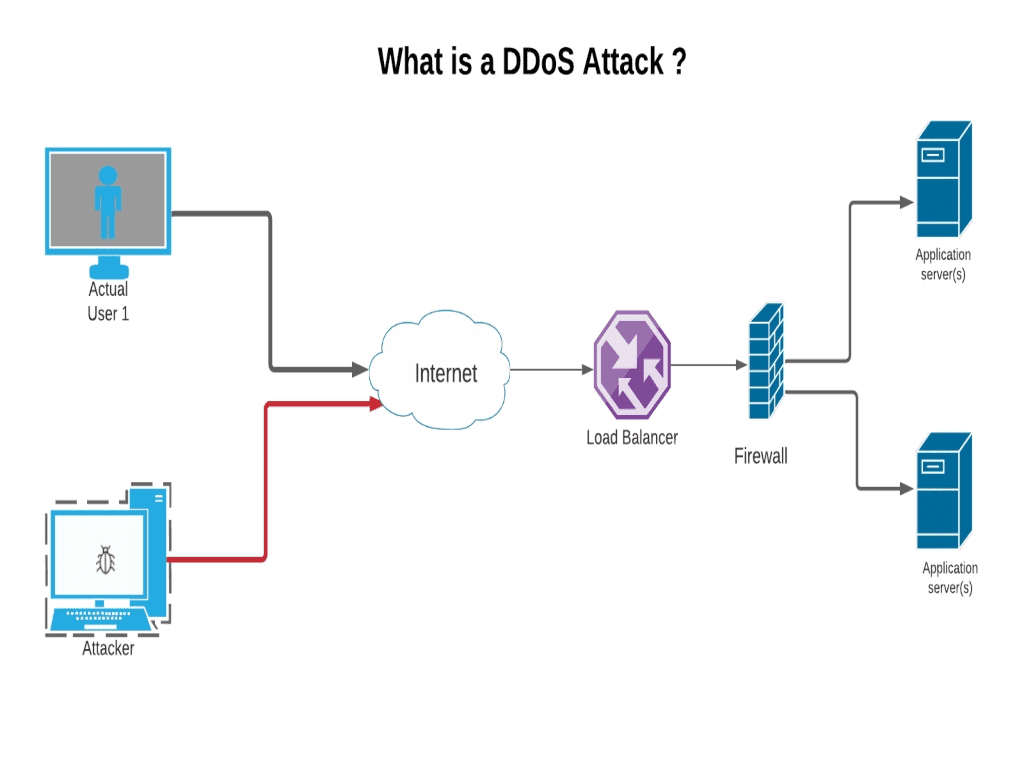
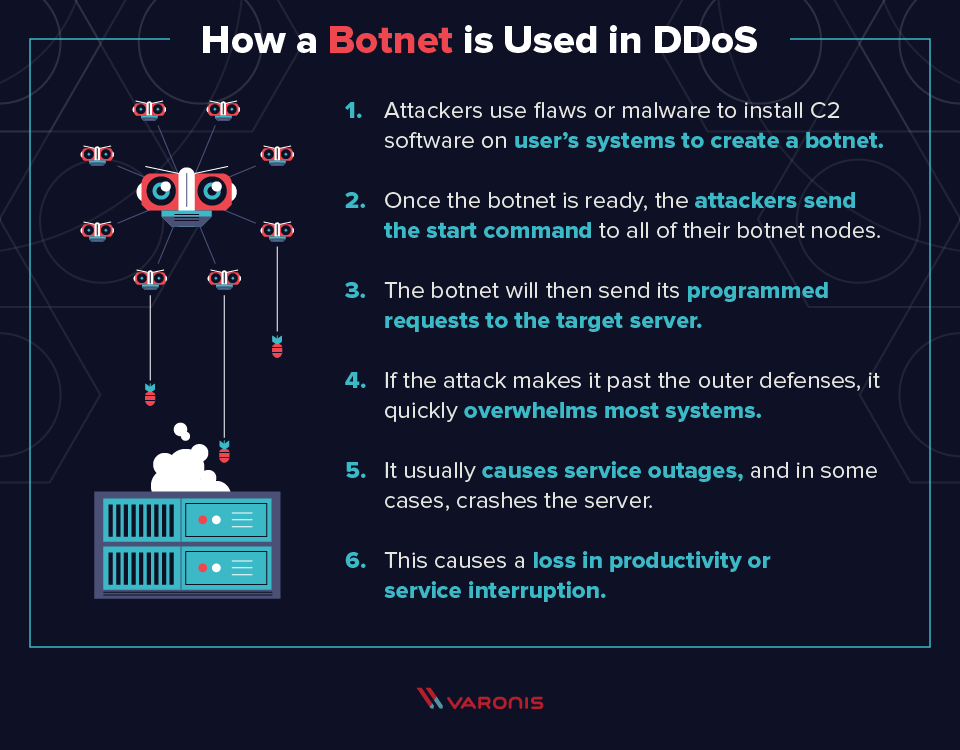
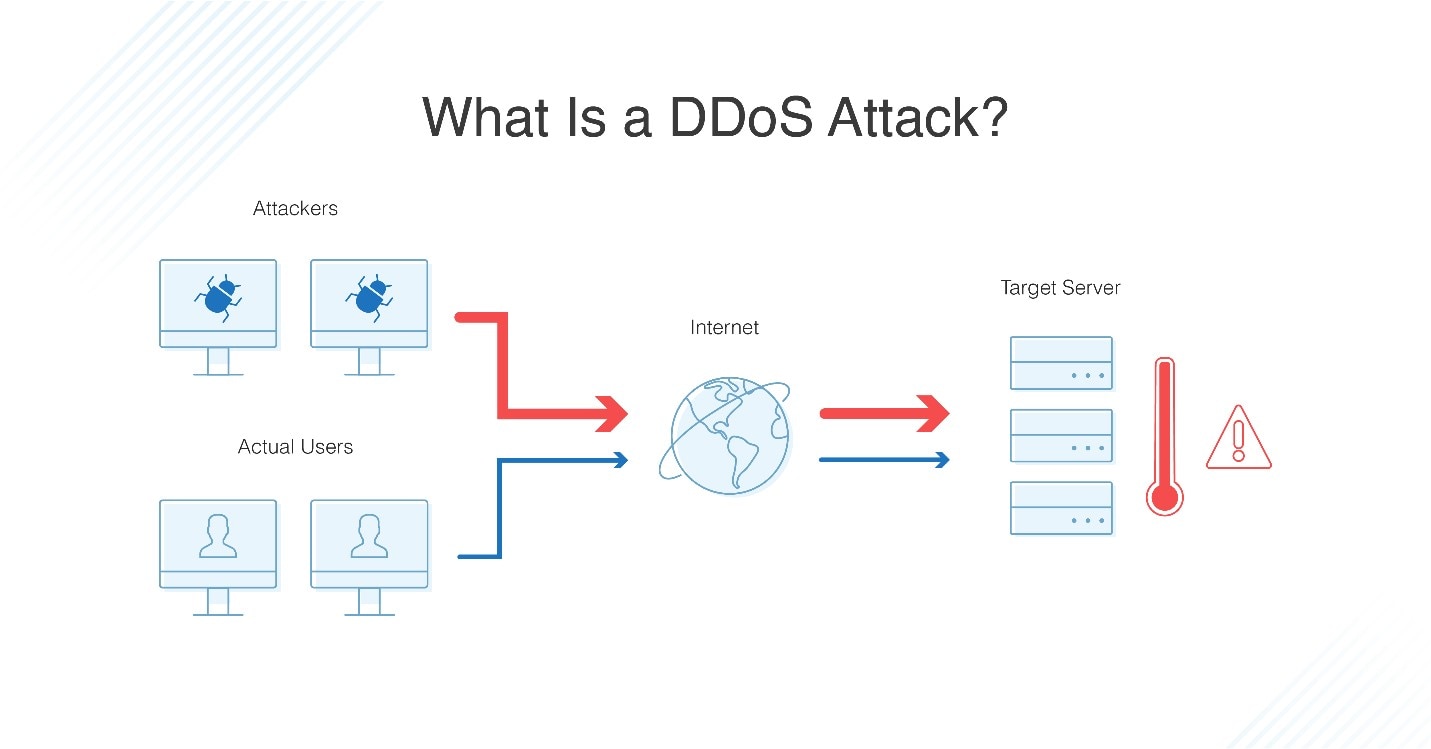
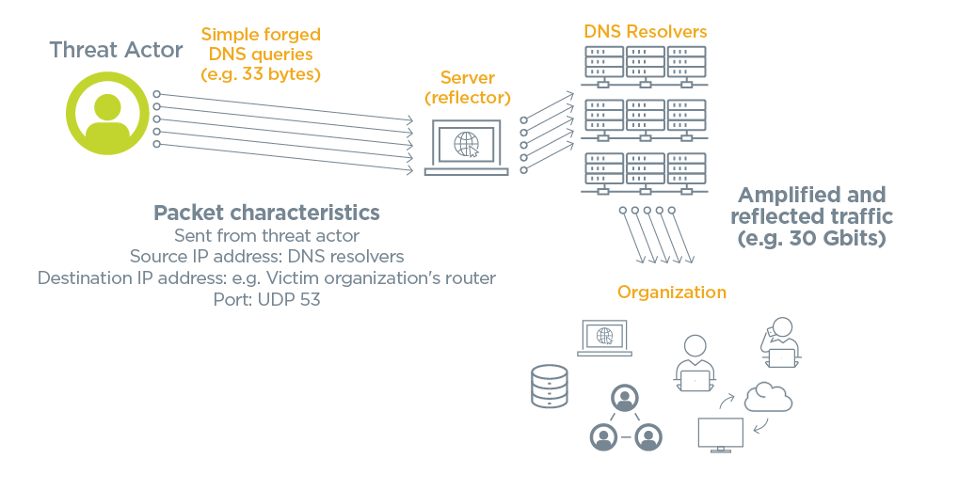
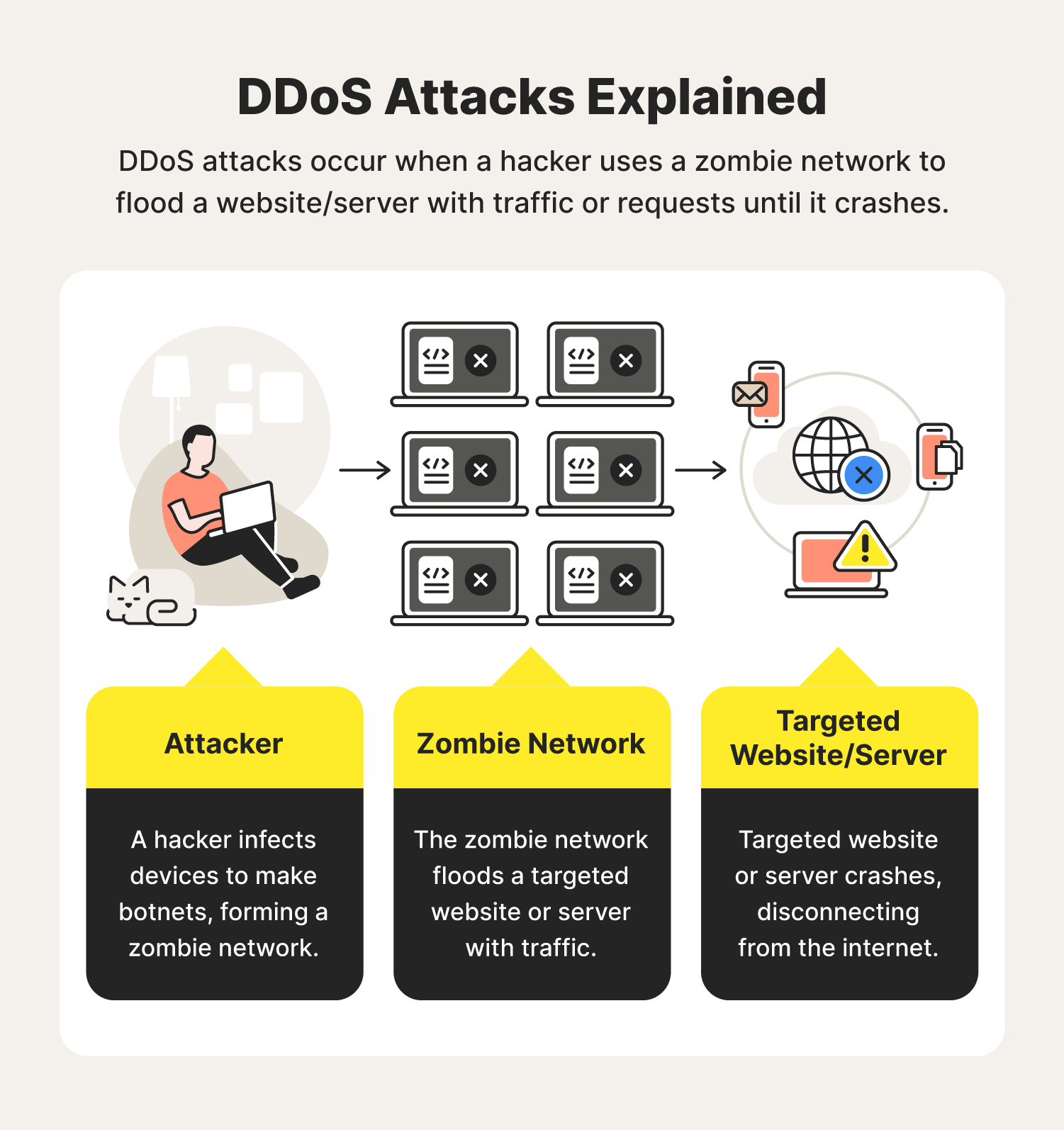
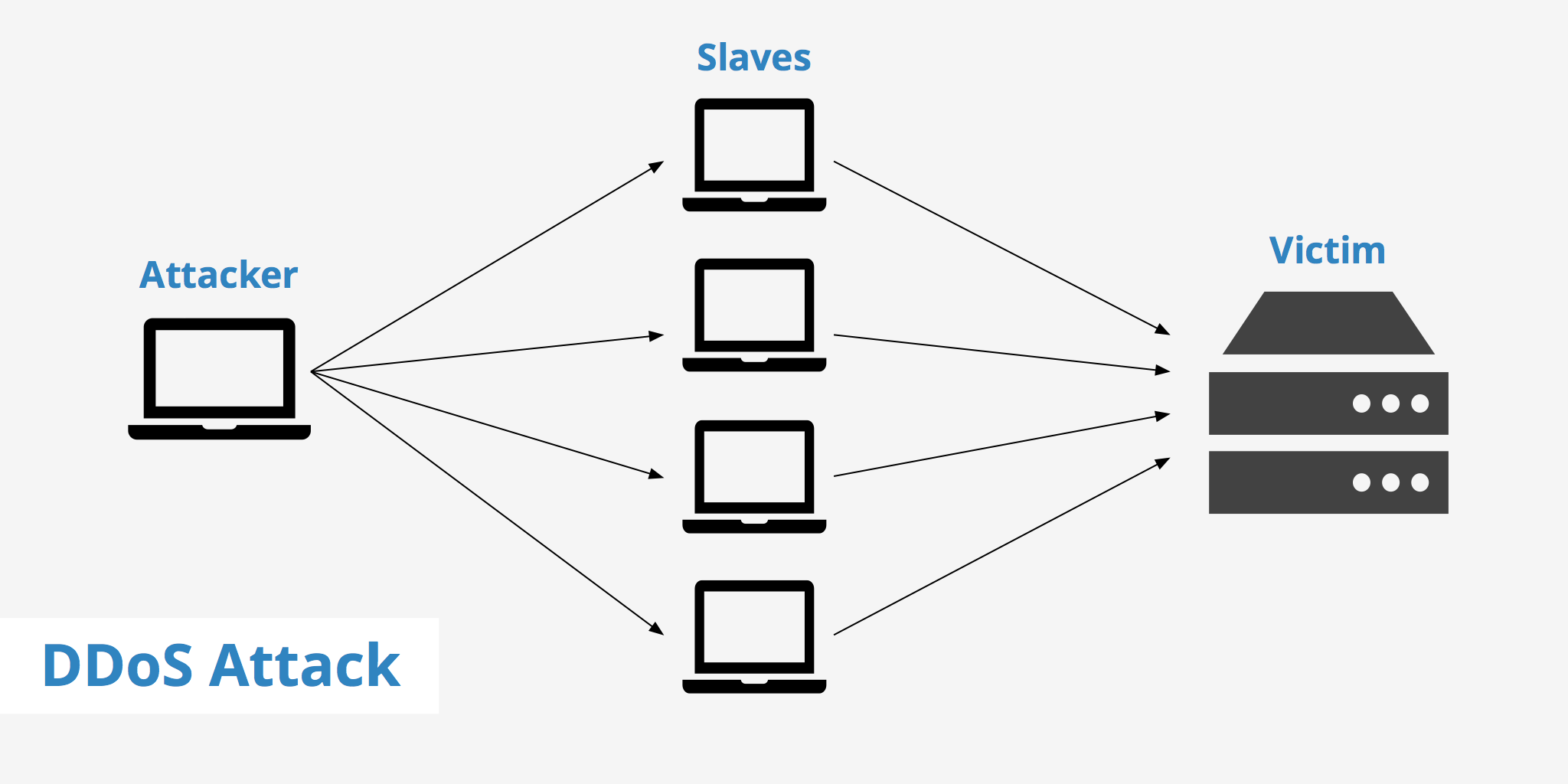
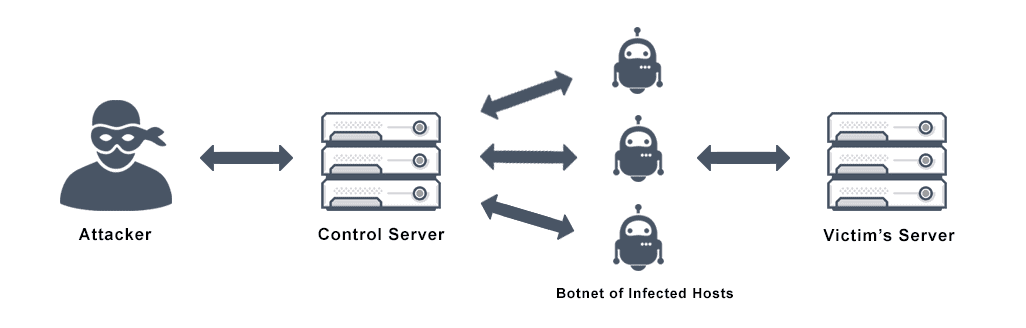
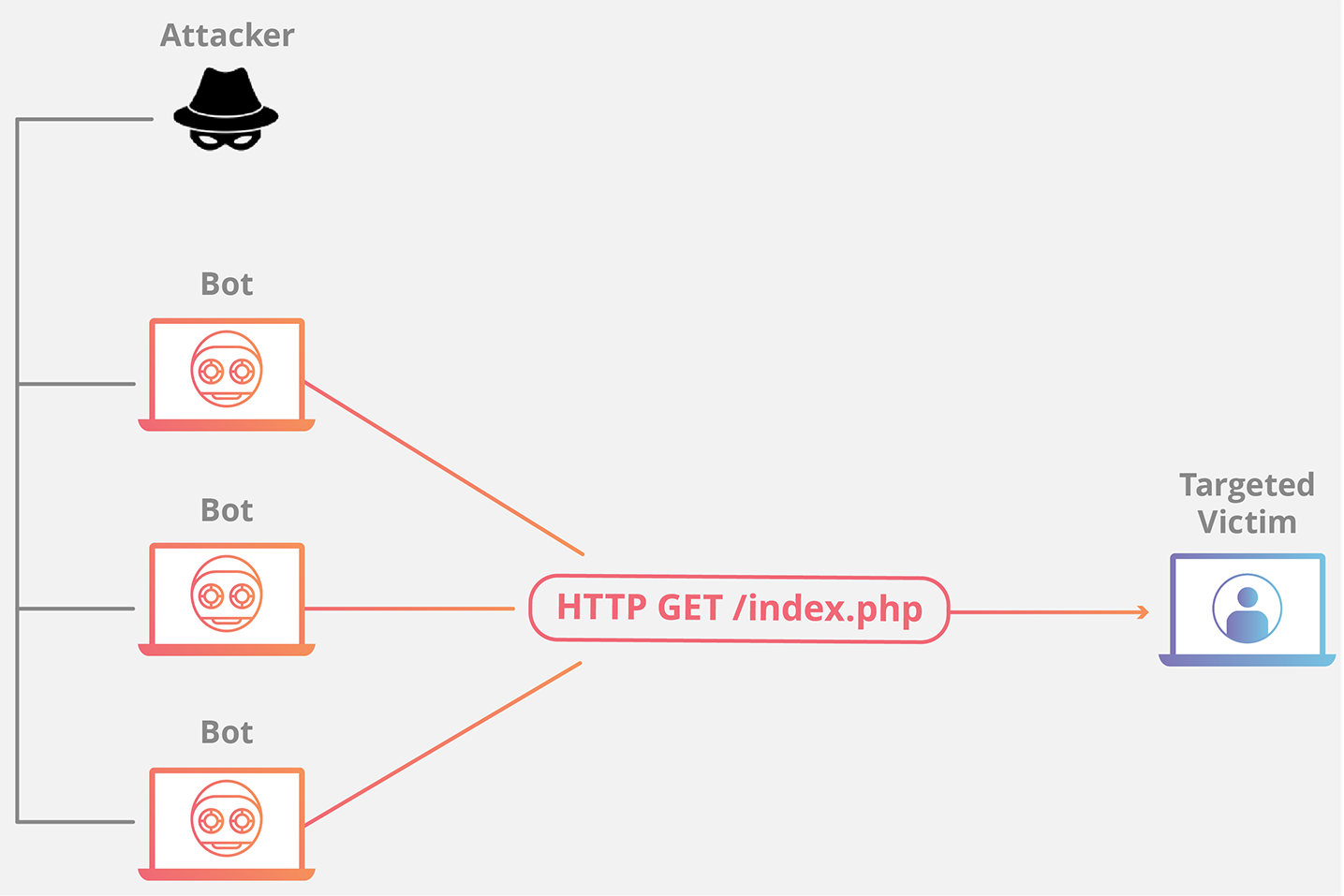
Step 1) you need to disable the syncookie in your system to perform the syn flooding attack. A basic ping flood attack can be accomplished. Here, to launch a distributed denial of service attack, in the ddos master system, the attacker uses botnets to affect and then control many computers and then attack a single system.
1.) low orbit ion cannon (loic) low orbit ion canon is a software that can. Open the task manager on the computer. Depending on the attack vector, dos attacks either seek to flood or to crash a system.
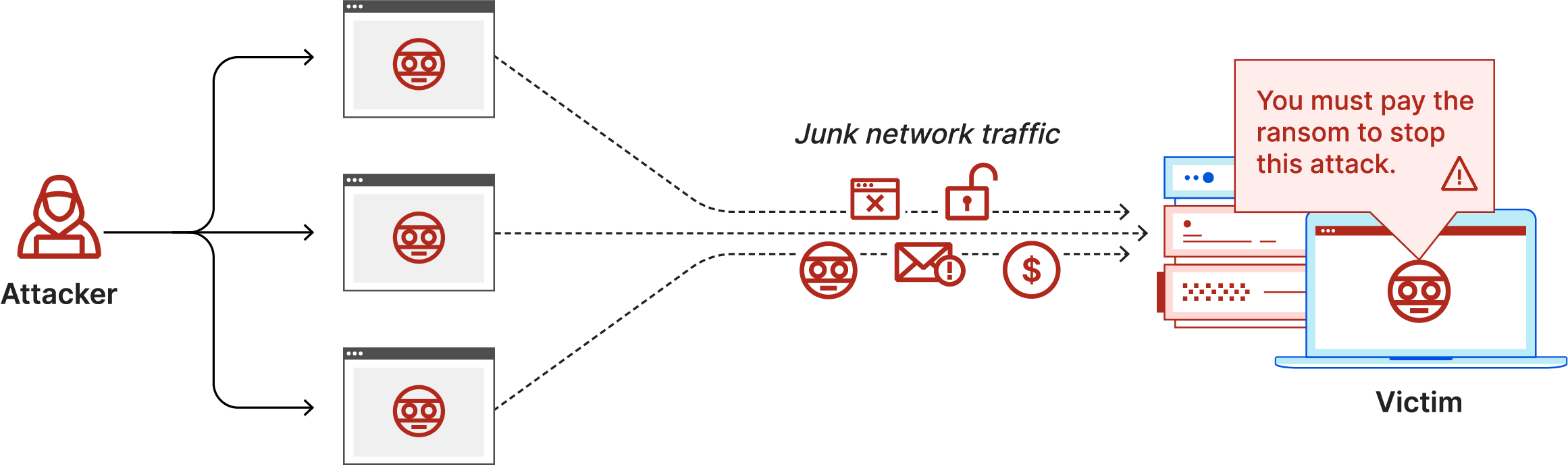
A multitude of different dos attacks exists. The first — and most popular — strategy is flooding: There are many ways of doing a ddos attack try them on your server or website never try them on other websites.
How to perform a ddos attack on a website using cmd 1. The more you know about what normal inbound traffic looks like, the quicker you'll spot the start of a ddos attack. You will notice six tabs.
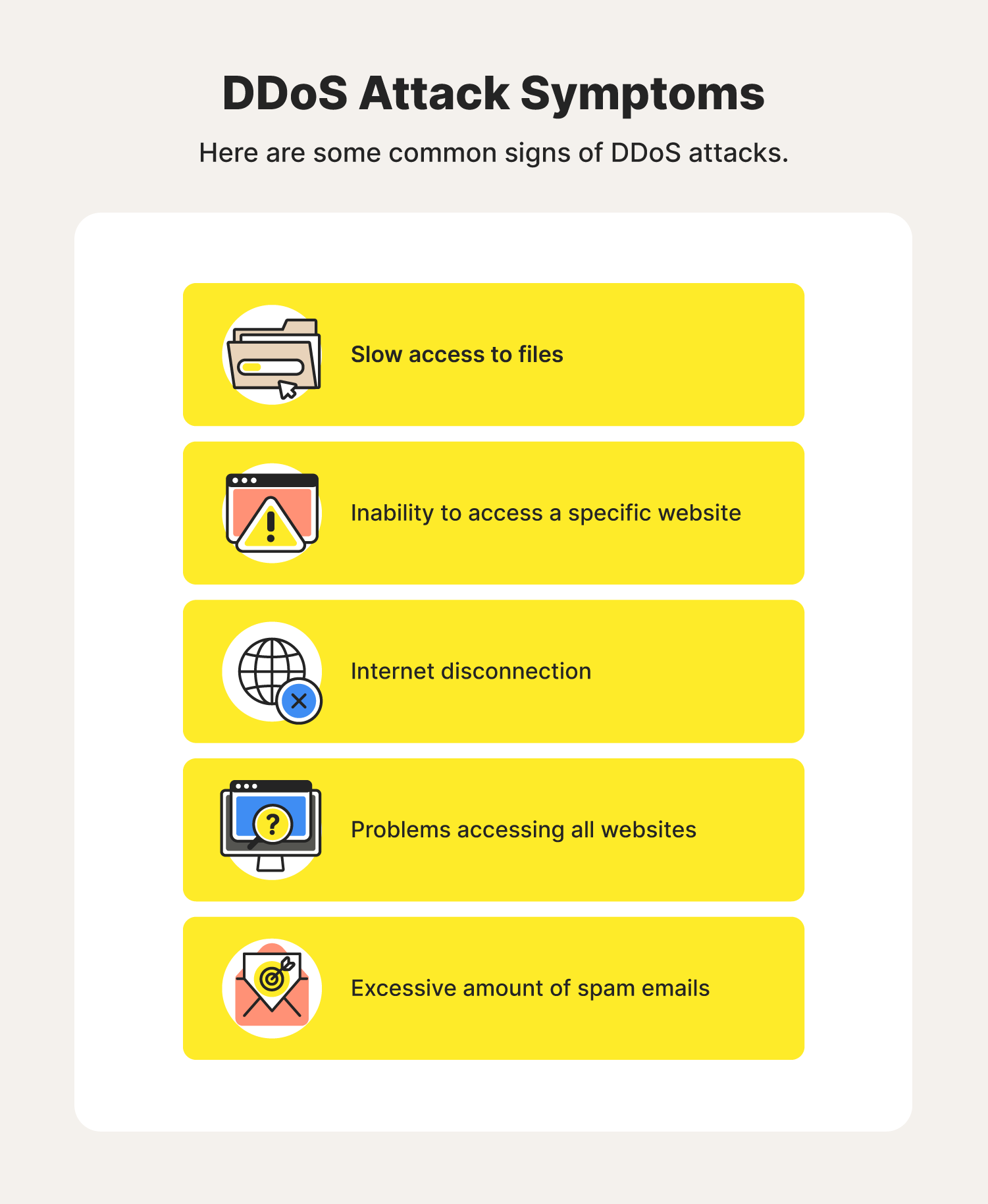
503 “service unavailable” errors should start around this time. Identify gaps in security and assess potential threats to your setup. Generally, this requires a fully managed solution which ensures that the network’s security posture is always effective and up.
They can be very simple; Dos attacks accomplish this disruption by sending malicious traffic from a single machine — typically a computer. The tool takes the url of.
Dos attacks use two primary strategies to accomplish that goal. Overwhelming a device or network with traffic. Next, verify it is correct and.
The three main types of dos attacks are:. Start by selecting a target for attack by entering the url or i.p. Immediate and automated updates as new forms of attack arise.
It is one of the free ddos attack tools specifically used to generate.
![What Is A Dos Attack And How To Dos Someone [Ping Of Death]](https://www.guru99.com/images/EthicalHacking/DOS_Attacks3.png)
![What Is A Dos Attack And How To Dos Someone [Ping Of Death]](https://www.guru99.com/images/EthicalHacking/DOS_Attacks.jpg)
![What Is A Dos Attack And How To Dos Someone [Ping Of Death]](https://www.guru99.com/images/EthicalHacking/DOS_Attacks4.png)

![What Is A Dos Attack And How To Dos Someone [Ping Of Death]](https://www.guru99.com/images/EthicalHacking/DOS_Attacks1.png)
![What Is A Dos Attack And How To Dos Someone [Ping Of Death]](https://www.guru99.com/images/EthicalHacking/DOS_Attacks5.png)